AI is everywhere now. It writes emails, edits photos, suggests videos, and finishes sentences you did not plan to type. All of that convenience comes at a cost, because these systems often run on personal data. Names, habits, voice clips, and search behavior quietly power the magic behind the screen.
The big question is simple but uncomfortable: should you really hand over that much of yourself? Trusting AI is not a yes or no situation. It is more like lending your car to someone you barely know. Sometimes it works out fine. Other times, you notice the fuel tank is empty, and the seat is pushed way back.
What Kind of Data AI Actually Collects
AI does not just look at what you type. It also pays attention to how you type, how long you pause, and what you ignore. Small details stack up fast and form patterns that feel personal, even if your name is missing. This data helps systems improve, but it also builds a quiet profile behind the scenes.
Voice assistants keep audio samples. Image tools retain metadata. Over time, these pieces paint a clear picture of habits and preferences. AI companies often say the data is used to improve performance. That can be true while still raising eyebrows. Improvement usually means storage, analysis, and reuse. Once data enters that loop, control becomes fuzzy.
Why Convenience Makes Trust Feel Easier Than It Should

AI tools save time, and time is precious. When something works smoothly, people stop asking questions. That comfort can lower skepticism faster than any policy document. Convenience has a sneaky way of dulling caution. There is also the illusion of distance. Data feels abstract, like numbers floating somewhere far away.
In reality, it often sits on servers tied to business goals. That gap between feeling and fact is where trust gets stretched thin. People rarely read terms before clicking agree. Even fewer revisit them later. That habit shifts power away from users without much resistance. It is not careless, just human.
Who Really Has Control Once Data Is Shared
After the data is uploaded, ownership gets blurry. Users may create the content, but platforms often decide how it is stored and processed. Access rules can change quietly over time. What felt private today might feel exposed tomorrow. Regulations exist, but enforcement varies by region.
Some companies act responsibly. Others test limits until someone pushes back. Users usually hear about issues after problems surface. Control also depends on deletion policies. Removing an account does not always erase everything. Copies, backups, and trained models may still carry traces. That reality surprises many people.
How to Use AI Without Giving Away the Farm

Using AI safely is about balance, not fear. You do not need to avoid it completely. You just need boundaries. Think before sharing personal stories, sensitive files, or identifying details. That’s why you need to separate tools by purpose. Use one for casual tasks and another for work. Avoid mixing personal and professional data in the same space. That simple habit reduces risk without much effort. Settings matter more than people think. Privacy options, history controls, and data retention toggles exist for a reason. A few minutes of setup can save months of regret later.
So, Should You Trust AI With Your Data?
Trust should be conditional. AI is powerful, but it is not a friend. Use AI with intention, not autopilot. Share what is needed and nothing extra. When trust is treated like a dial instead of a switch, users stay in control. In the end, smart use beats blind faith every time.…

















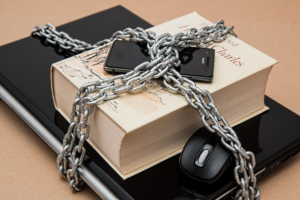 Encryption is a fundamental technique used to enhance security and protect sensitive data. It involves the process of converting plain text into unreadable ciphertext, making it difficult for unauthorized individuals to access or interpret the information. One popular encryption method is called symmetric encryption, where the same key is used for both encrypting and decrypting data. This type of encryption is efficient but can pose challenges in securely sharing the key between parties. Another widely used encryption approach is asymmetric encryption, which utilizes a pair of keys – one public and one private. The public key is shared openly, while the private key remains confidential. This method offers stronger security as only the corresponding private key can decrypt the encrypted data.
Encryption is a fundamental technique used to enhance security and protect sensitive data. It involves the process of converting plain text into unreadable ciphertext, making it difficult for unauthorized individuals to access or interpret the information. One popular encryption method is called symmetric encryption, where the same key is used for both encrypting and decrypting data. This type of encryption is efficient but can pose challenges in securely sharing the key between parties. Another widely used encryption approach is asymmetric encryption, which utilizes a pair of keys – one public and one private. The public key is shared openly, while the private key remains confidential. This method offers stronger security as only the corresponding private key can decrypt the encrypted data.

 One of the essential benefits of Bitcoin is its decentralization. Unlike traditional currencies, which are regulated by central banks, Bitcoin is not subject to government control.
One of the essential benefits of Bitcoin is its decentralization. Unlike traditional currencies, which are regulated by central banks, Bitcoin is not subject to government control. iPhone spy apps are software programs that allow you to track and monitor activity on an iPhone. You can use them for various purposes, such as watching your children’s online activity, monitoring employees’ phone use, or even locating a lost or stolen iPhone. The best iPhone spy apps will give you access to a wide range of information, including text messages, phone calls, web history, location data, and more.
iPhone spy apps are software programs that allow you to track and monitor activity on an iPhone. You can use them for various purposes, such as watching your children’s online activity, monitoring employees’ phone use, or even locating a lost or stolen iPhone. The best iPhone spy apps will give you access to a wide range of information, including text messages, phone calls, web history, location data, and more. Once you’ve decided which iPhone spy app is right for you, the next step is to install it on the target device. This process can vary depending on the app, but most are relatively easy to set up. Once the app is installed, it will begin tracking and monitoring all activity on the phone.
Once you’ve decided which iPhone spy app is right for you, the next step is to install it on the target device. This process can vary depending on the app, but most are relatively easy to set up. Once the app is installed, it will begin tracking and monitoring all activity on the phone. There are many benefits to using iPhone spy apps. Some of the main advantages include monitoring your children’s online activity, tracking employees’ phone use, and locating lost or stolen iPhones. You can also use them for various other purposes, such as monitoring what websites someone is visiting or who they are contacting through their cell phone.
There are many benefits to using iPhone spy apps. Some of the main advantages include monitoring your children’s online activity, tracking employees’ phone use, and locating lost or stolen iPhones. You can also use them for various other purposes, such as monitoring what websites someone is visiting or who they are contacting through their cell phone.
 It is also crucial to consider the type of service offered by a tech repair service provider. Different service providers tend to focus on offering several services. They may include phone screen repair and replacements, among many other services. You should only select a tech repair service provider that offers the service you need.
It is also crucial to consider the type of service offered by a tech repair service provider. Different service providers tend to focus on offering several services. They may include phone screen repair and replacements, among many other services. You should only select a tech repair service provider that offers the service you need.
 When sound leaves the guitar, it hits the reverb pedals, and comes back to you in echoes. These reverberations are what you are supposed to use in order to make the sound richer and fuller. For instance, while one sound looks too ordinary, several interconnecting echoes will make it sound much better. It is a trick that is used by musicians to make great beats on a budget. What makes it even better is that to achieve your desired tone, all that you have to do is to find a reverberation level that best suits your plans.
When sound leaves the guitar, it hits the reverb pedals, and comes back to you in echoes. These reverberations are what you are supposed to use in order to make the sound richer and fuller. For instance, while one sound looks too ordinary, several interconnecting echoes will make it sound much better. It is a trick that is used by musicians to make great beats on a budget. What makes it even better is that to achieve your desired tone, all that you have to do is to find a reverberation level that best suits your plans. You have to think about the performance of a reverb pedal before choosing it for your audio project. As you will find out, there is a difference in what you can expect from various brands. For instance, while others are easy to use, some may require you to be a little skilled to utilize them. Although these items cost significantly less than most of the other options that you will find out there, you will be surprised to find out that they can outperform all of them if they are used rightly. Therefore, you need to focus on the performance.
You have to think about the performance of a reverb pedal before choosing it for your audio project. As you will find out, there is a difference in what you can expect from various brands. For instance, while others are easy to use, some may require you to be a little skilled to utilize them. Although these items cost significantly less than most of the other options that you will find out there, you will be surprised to find out that they can outperform all of them if they are used rightly. Therefore, you need to focus on the performance.